Stephan Berger@malmoeb
Sep 23, 2022
4 tweets
1/ #ThreatHunting:
In a compromised network, we saw the following request in the proxy logs:
www.advanced-ip-scanner[.]com/checkupdate.php?[..]
This scanner is trendy among ransomware groups and has been mentioned in reports by @The DFIR Report, among others. [1] 

2/ This HTTP request can now be used very well for an alert.
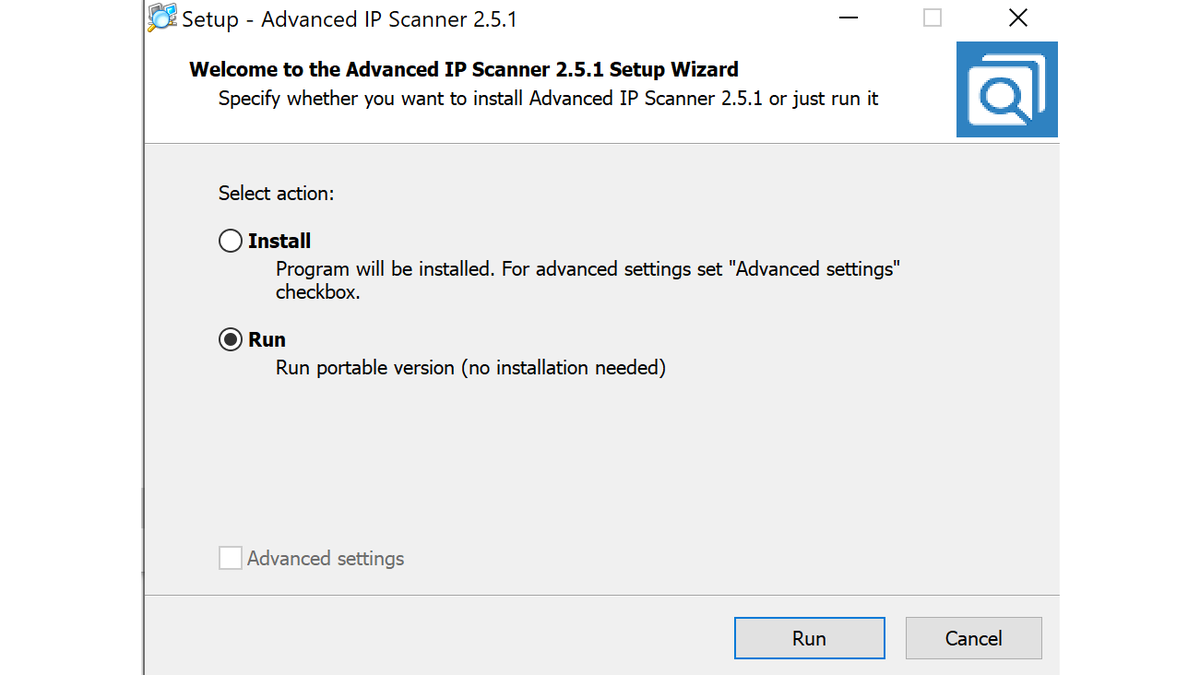
Or better, collect and monitor all your DNS logs, because a DNS request will still go out if the Advanced IP Scanner is run without an installation (portable version).
An excellent opportunity for detection.
3/ You can see the DNS request for the domain www.advanced-ip-scanner[.]com below.
4/ DFIR Tip:
Inside the registry (HKCU\Software\Famatech\advanced_ip_scanner\State) we can find interesting forensic artifacts like the last scanned range.  Reference:
[1] twitter.com/TheDFIRReport/
Reference:
[1] twitter.com/TheDFIRReport/
 Reference:
[1] twitter.com/TheDFIRReport/
Reference:
[1] twitter.com/TheDFIRReport/ 
The DFIR Report@TheDFIRReport
Dec 13 21
View on Twitter
Diavol Ransomware
 Initial Access: Zip->ISO loading BazarLoader
Initial Access: Zip->ISO loading BazarLoader
 Discovery: Net, Ping, AdFind, Advanced IP Scanner, ShareFinder
Discovery: Net, Ping, AdFind, Advanced IP Scanner, ShareFinder
 C2: #CobaltStrike & #BazarLoader
C2: #CobaltStrike & #BazarLoader
 Lateral Movement: RDP, AnyDesk
Lateral Movement: RDP, AnyDesk
 Exfil: FileZilla, ufile
Exfil: FileZilla, ufile
 Impact: Diavol ransomware
thedfirreport.com/2021/12/13/dia
Impact: Diavol ransomware
thedfirreport.com/2021/12/13/dia
 Initial Access: Zip->ISO loading BazarLoader
Initial Access: Zip->ISO loading BazarLoader
 Discovery: Net, Ping, AdFind, Advanced IP Scanner, ShareFinder
Discovery: Net, Ping, AdFind, Advanced IP Scanner, ShareFinder
 C2: #CobaltStrike & #BazarLoader
C2: #CobaltStrike & #BazarLoader
 Lateral Movement: RDP, AnyDesk
Lateral Movement: RDP, AnyDesk
 Exfil: FileZilla, ufile
Exfil: FileZilla, ufile
 Impact: Diavol ransomware
thedfirreport.com/2021/12/13/dia
Impact: Diavol ransomware
thedfirreport.com/2021/12/13/dia
Stephan Berger
@malmoeb
Head of Investigations @InfoGuardAG • #DFIR • Threat Hunting • Azure & Active Directory Fanboy • OSCP, GXPN, GCIA, GCFA, GSE
Missing some tweets in this thread? Or failed to load images or videos? You can try to .